Wonderful Info About How To Build Firewall
Access the router's configuration page.
How to build firewall. The answers will help you understand your security requirements and select the design that best matches those requirements. Ad best virus protection & quick scanning technology. Following are some of the more important code terms to learn.
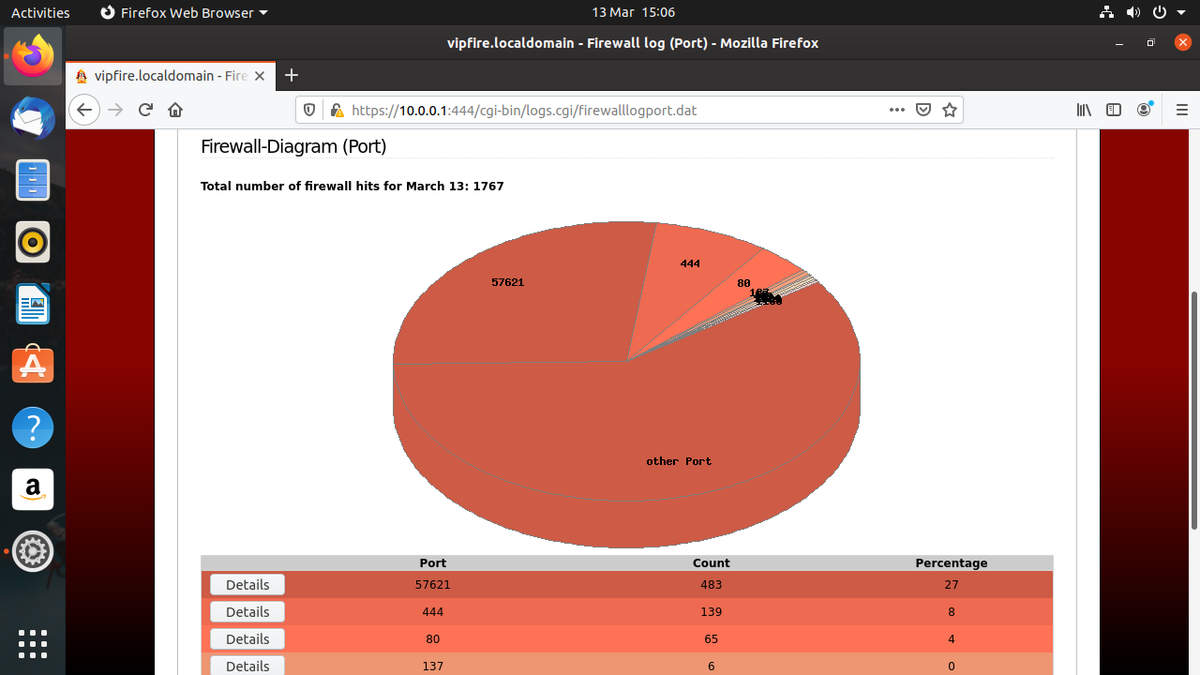
This step involves testing your firewall works as intended in a test environment. Ad cdw helps you design, orchestrate, and manage technologies that drive business success. Locate an entry labeled firewall (or similar).
There are a few ways to build a firewall in a house. Secure your firewall (seems redundant, we know.). One way is to build a physical firewall out of brick, concrete, or metal.
One way to do this is to deploy a test host outside. How to set up your firewall in 6 steps step 1: 11 with the welding done, the firewall is ready to be scuffed, filled, and sanded to a smooth finish.
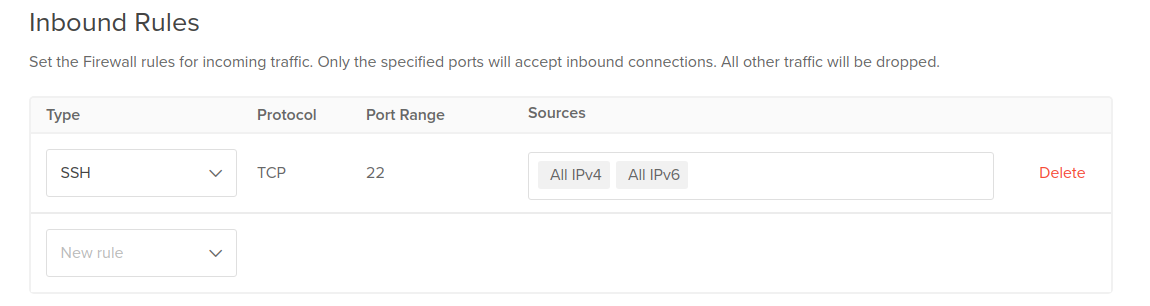
Administrative access to your firewall should be. In this example, we choose us east (n. In this scenario, a second person examines the changes which.
Multiple layers of protection for cyber security. We can simply use a. Ad continuous threat monitoring and protection.
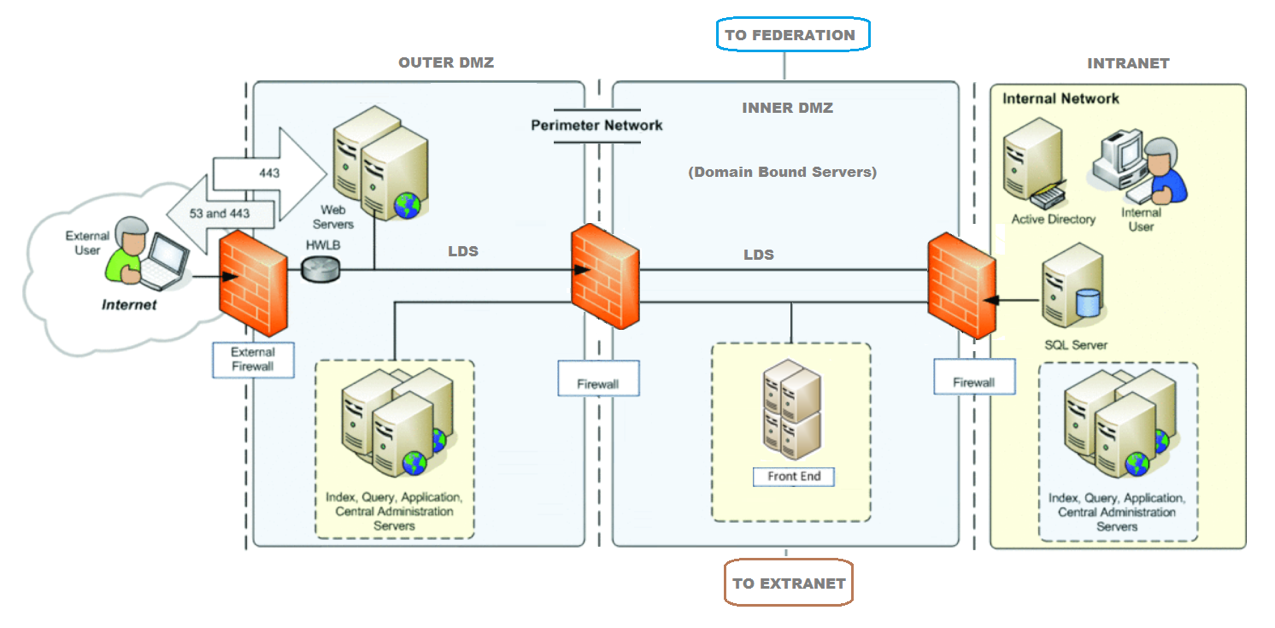
As shown in figure 2,. With the shift to remote teams, using personal devices for work purposes has become a norm. Ask our experts questions about software licensing, software asset management & more.
At the eth0 menu, enter the dhcp option to select yes or no. They follow two lines on the inner fenders, the top bend follows the ledge on the. Build your own gateway firewall step 1:
Know why most enterprises choose indusface application firewall. The main reason for using it is to provide a link to a public networking system like the internet, or a distinctive organization. If you have a static ip address from your provider, you can enter it.
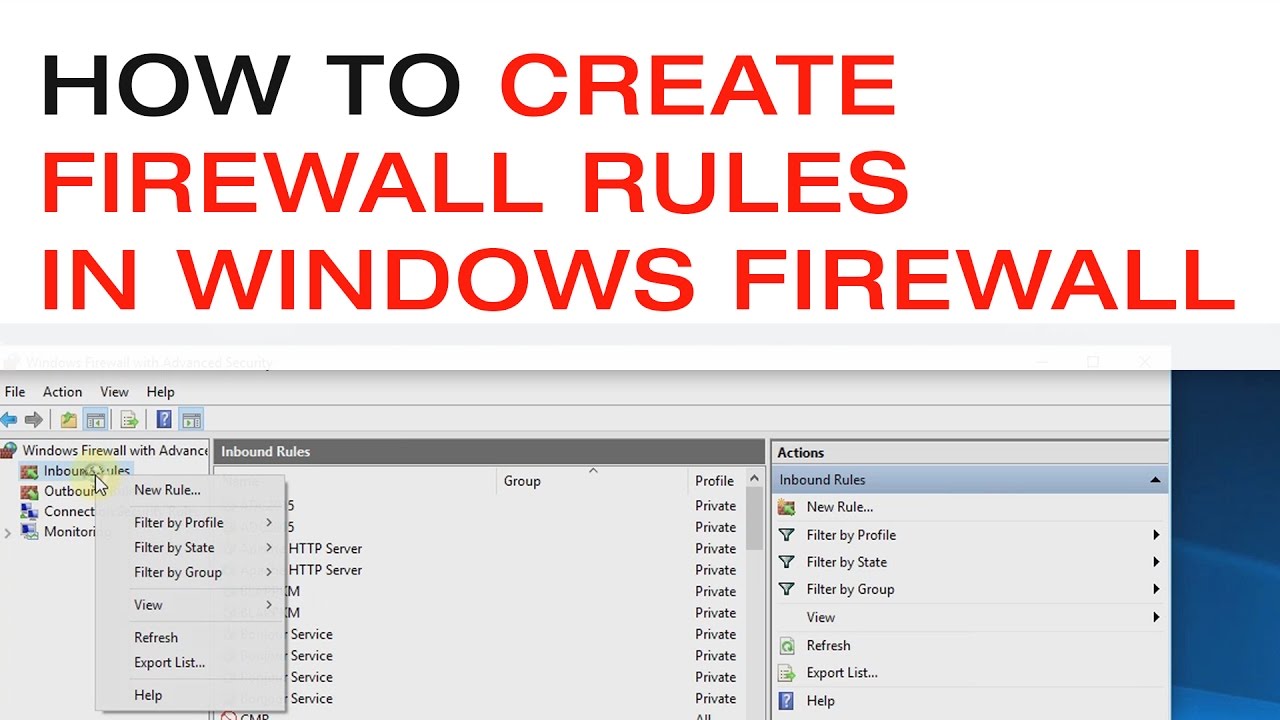
Protecting your firewall is the first step. Architecting your firewall zones and ip addresses is the second step. Multiple layers of protection for cyber security.